Remote Eavesdropping
You are here
Introduction
In 2013, the STAC approved a remote eavesdropping observing mode. This document lists the main features of the mode as implemented since tests carried out in 2012B. PI Procedures are detailed at the end of this page.
Eavesdropping IS:
- Added value only. All observations must be executable without eavesdropping, no observation should rely on it.
- Initiated by the observatory (advance warning of probability in the queue case, or definite date in the classical case, plus on-the-night notification by some method which would convey a password, probably one changed on an hourly basis).
- Ability to see, and comment on, target acquisitions.
- Ability to assess data quality quickly enough to allow useful changes to be made in the observing.
- Ability to understand what is happening in the observing at any given time.
- Ability to see: sequence executor.
- Ability to see: data reduction pipeline products.
- Ability to see: acquisition.
- Ability to request modifications to observation (change exposure time, re-arrange steps, change wavelength, add a filter, skip a previously included filter, etc). Must not significantly change the nightly queue plan in a way that the observer would not have done and must not redefine the observation in a way which might duplicate some other observation in the database. (Guidelines will be needed for the observer in these cases.)
- Ability to communicate: with observer (by phone, Skype to a single observer account, or Polycom from a defined remote ops center).
- Ability to see: TSD and/or ISD (this is non-essential).
- Ability to interact with raw data for their project (and associated calibrations) stored at the observator.
Eavesdropping IS NOT:
- Ability to override: queue decisions taken by the summit staff and/or QC. All queue choices will be made in the same way as normal. This includes rapid Targets of Opportunity, which will continue to interrupt the current observation even if that observation is being eavesdropped upon. In a marginal case, e.g. very thin cirrus, and where there is no direct impact on higher-priority programs, the PI may be asked if they wish to continue. If they say yes, despite the weather conditions being outside their formal requirements, a “PASS” flag will be placed on the data in the GSA.
- Ability to directly execute (start, stop etc.) the sequence.
- Ability to directly control the instrument.
- Ability to see the summit OT (because of confidentiality of other programs).
- Ability of PI to communicate with QC (the observer will do this in case of need).
- Allowed to result in additional staff hours at the observatory. In practice this means that it will not be used in classical runs unless the classical programme has already sent the PI or a Co-I to the summit.
- Allowed to result in reduced efficiency – emphasis remains on pre-preparation of observations. No preparation is done on the fly at night, and all time spent inspecting acquisition images etc. is charged to the PI’s programme.
- Allowed to produce additional work on QCs or staff queue observers.
- Applied to short observations (this is to avoid the overhead of contacting the PI, getting the eavesdropping session established etc. for an observation that may only take 15 minutes).
The Mode
All Band 1 and 2 PIs are invited to eavesdropping if they wish, via the PI email announcing that they have been granted time. If a PI chooses to eavesdrop, they enter their range of dates for multiple contact numbers in a google spreadsheet. Observers at the summit check this spreadsheet to see if a PI has an available contact for the current night.
On a given night, should the program come to the top of the queue and be identified in the plan as an eavesdropping program for the night, the PI or designated contact receives a phone call stating that observations are about to begin. They open Skype on a browser, connect to the summit and to a FITS storage server, and take part in the observation, including watching and commenting on acquisitions, inspecting data frames and commenting on whether to continue or terminate an observation. Note that the QCs will not always schedule a program for eavesdropping on a given night, even though it has that "status". For example, they may be guided by the weather forecast and we will also attempt to avoid scheduling sessions back to back to give the observer a breather. So data may be taken on an eavesdropping program without a call being made (this is also consistent with observers having discretion over calling, and with the first point in "IS", above).
To avoid confidentiality issues and debates between PIs In the course of any given night, only one program will be invited to eavesdrop at a time. To ensure quick decision making and as easy as possible a technical interface, only one eavesdropping channel will be open on a given programme at a time.
Brief records are kept (in the night log) of the key points of the dialogue between the observer and the PI.
PI Procedures
Initial contact
PIs will be invited to participate in eavesdropping in the initial PI email announcing they have been allocated observing time. The deadline for signing up for eavesdropping is the Phase II submission deadline. If you wish to take part, you will be asked to send the contact details for up to three eavesdroppers:
- Name
- email address
- telephone number
Note that you can designate up to three sets of details; these may be used to give three different contact numbers for yourself, to be used at different times in the semester, three different co-Is to cover different ranges of nights,or some combination of these. We use these to set up our dial-up calls that will be used to make initial contact on any given night. The three contacts are labelled "a", "b" and "c" respectively; please refer to them as such in your emailed response.
Specifying contact availability
You will receive a link to a google spreadsheet in the initial email. This is where you tell us who is available and when. The data entry sheet looks like the following:
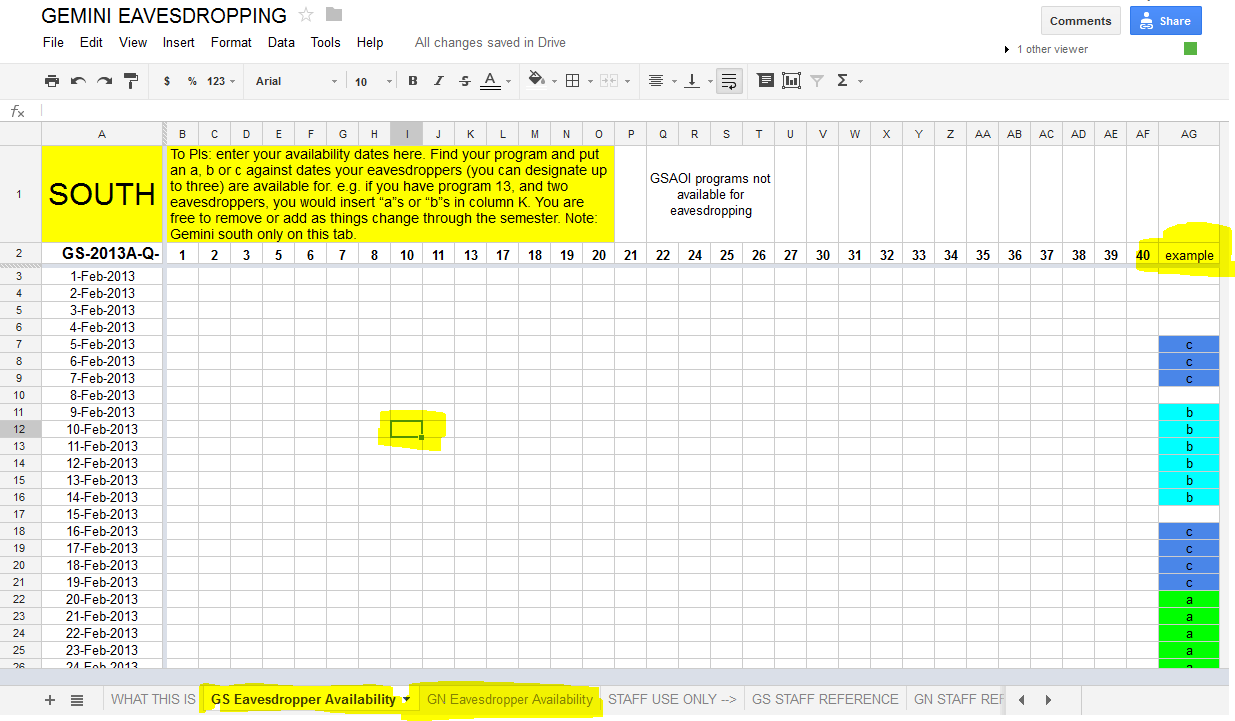
All you need to do is locate the "Availability" tab (bottom of the browser window) for the telescope you wish to eavesdrop at, and enter "a", "b" or "c" into each date on which your contacts are available (only one contact per night). Please be sure to consider the target observability and enter contacts, if possible, at the earliest possible date - your program may well be observed as soon as the targets become available.
